Secret Scanning Guide: Precogs Adaptive Intelligence vs. TruffleHog
Advanced PII & Secrets Security
Secret detection is critical for preventing credential leaks that can lead to data breaches, financial losses, and compliance violations. This article compares Precogs Adaptive Intelligence with TruffleHog, one of the most popular security tools, highlighting the strengths and trade-offs of each approach.
| Metric | Precogs Identity Protection | TruffleHog v3 |
|---|---|---|
| Detection Patterns | 816+ (50+ built-in + 761 from database) | 800+ verified detectors |
| Detection Method | Regex + Entropy + ML + Validation | Regex + Verification API |
| Context Awareness | ✅ File type, surrounding code | ✅ Git history |
| Live Verification | ✅ Optional (Enterprise) | ✅ Built-in |
| False Positive Rate | ~1-3% (with validation) | ~5-10% (without verification) |
| Processing Speed | 0.002s avg (regex) / 0.1s (ML) | 0.01-0.05s per file |
| SVG/XML Handling | ✅ Context-aware filtering | ⚠️ Can produce false positives |
The High Stakes of Secret Sprawl: In 2024, credential leakage remains the #1 entry point for ransomware. While traditional tools can find simple patterns, they often struggle with the "last mile"—obfuscated keys, framework-specific secrets, and high-noise environments that lead to security alert fatigue.
Detection Methodologies
PrecisionShift™: Intelligent Multi-Layer Defense
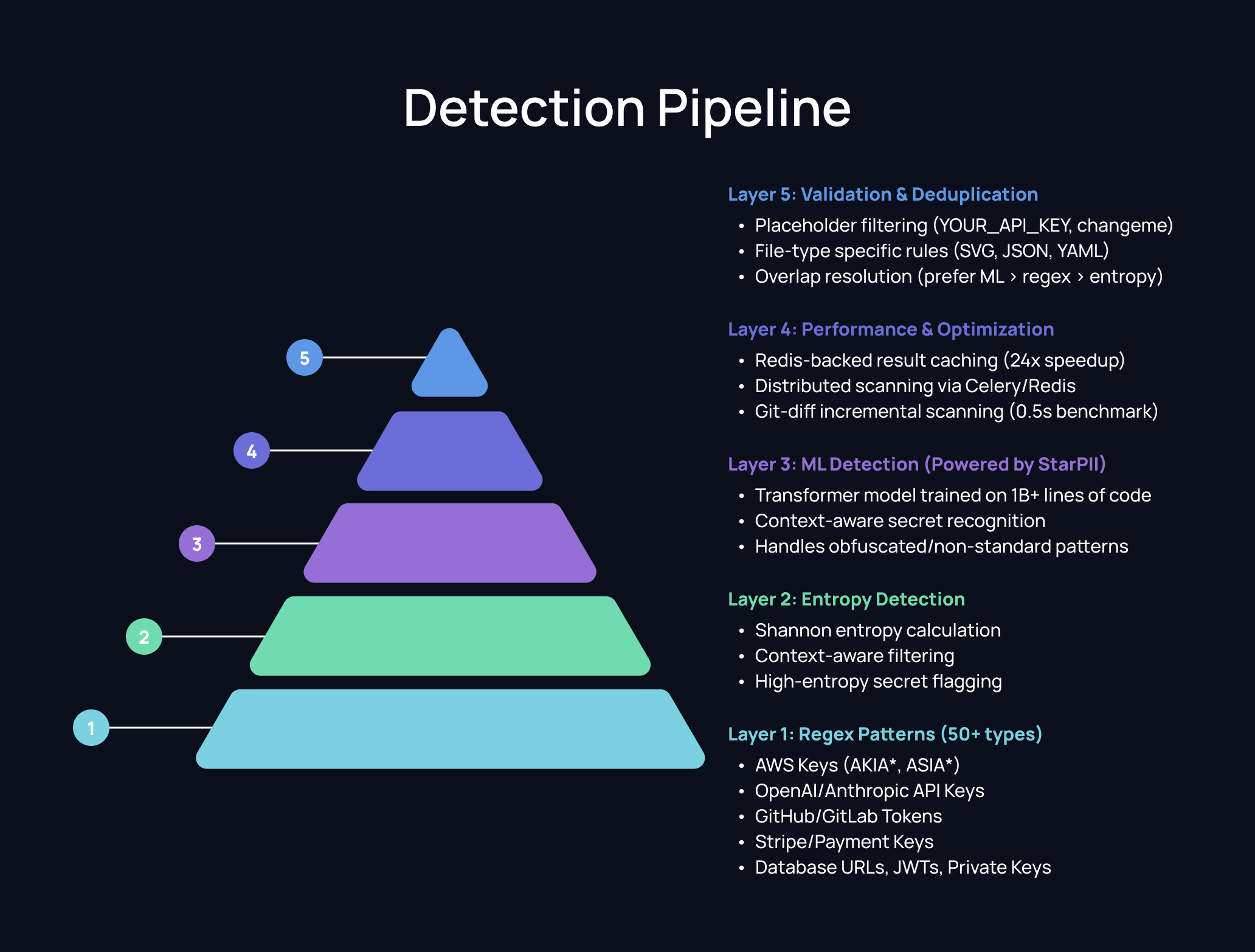
Our pipeline uses a multi-layer detection strategy:
Pattern Coverage Comparison
Cloud Provider Credentials
| Secret Type | Our Approach | TruffleHog | Notes |
|---|---|---|---|
| AWS Access Key | ✅ AKIA*, ASIA* | ✅ Verified | Both detect + TH verifies |
| AWS Secret Key | ✅ Context-based | ✅ Verified | We use surrounding context |
| GCP API Key | ✅ AIza* | ✅ Verified | Similar patterns |
| GCP Service Account | ✅ JSON structure | ✅ Verified | We detect JSON pattern |
| Azure Secret | ✅ Context-based | ✅ Verified | TH has more Azure types |
| Azure Connection String | ✅ Full pattern | ✅ Verified | Both cover well |
AI/ML API Keys
| Secret Type | Our Approach | TruffleHog | Notes |
|---|---|---|---|
| OpenAI API Key | ✅ sk-*, sk-proj-* | ✅ | We cover v1 and v2 formats |
| Anthropic API Key | ✅ sk-ant-* | ⚠️ Limited | We have explicit pattern |
| HuggingFace Token | ✅ hf_* | ✅ | Both cover |
| Replicate API Key | ✅ r8_* | ⚠️ Limited | We have explicit pattern |
| Cohere API Key | ✅ Context-based | ⚠️ Limited | We detect via context |
CI/CD & Version Control
| Secret Type | Our Approach | TruffleHog | Notes |
|---|---|---|---|
| GitHub PAT | ✅ All types (ghp_, gho_, ghu_, ghs_, ghr_) | ✅ Verified | TH verifies via API |
| GitHub App Token | ✅ github_pat_* | ✅ Verified | Both cover |
| GitLab Token | ✅ glpat-*, glcbt-* | ✅ Verified | Both cover well |
| Bitbucket Token | ✅ Context-based | ✅ Verified | TH has more patterns |
| CircleCI Token | ✅ Context-based | ✅ Verified | TH verifies |
| NPM Token | ✅ npm_* | ✅ | Both detect |
| PyPI Token | ✅ pypi-* | ✅ | Both detect |
Payment Processors
| Secret Type | Our Approach | TruffleHog | Notes |
|---|---|---|---|
| Stripe Secret Key | ✅ sk_live_*, sk_test_* | ✅ Verified | TH distinguishes live/test |
| Stripe Webhook | ✅ whsec_* | ✅ | Both detect |
| Square Token | ✅ EAAA* | ✅ Verified | Both cover |
| PayPal Secret | ✅ Context-based | ✅ Verified | TH has dedicated detector |
| Braintree Token | ✅ Explicit pattern | ⚠️ Limited | We have explicit pattern |
Real-World Examples
Example 1: AWS Credentials in Config File
Input File (config.env):
Production configuration:
AWS_ACCESS_KEY_ID=AKIAIOSFODNN7EXAMPLE AWS_SECRET_ACCESS_KEY=wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY DATABASE_URL=postgresql://admin:SuperSecret123@prod-db.company.com:5432/main
Our Detection:
[ {"label": "AWS_ACCESS_KEY", "value": "AKIA***LE", "confidence": 0.90, "source": "regex"}, {"label": "AWS_SECRET_KEY", "value": "wJal***EY", "confidence": 0.85, "source": "regex"}, {"label": "DATABASE_URL", "value": "post***in", "confidence": 0.90, "source": "regex"} ]
Analysis:
- ✅ Both detect all three secrets
- ✅ Our approach masks values for security
- ⚠️ TruffleHog doesn't detect DATABASE_URL by default
Example 2: AI/ML API Keys in Code
Input File (app.py):
import openai import anthropic **API Configuration** openai.api_key = "sk-proj-abc123def456ghi789jkl012mno345pqr678stu901vwx234yz" claude_key = "sk-ant-api03-abcdefghijklmnopqrstuvwxyz0123456789ABCDEFGH" hf_token = "hf_abcdefghijklmnopqrstuvwxyz123456"
Our Detection:
[ {"label": "OPENAI_API_KEY_V2", "value": "sk-p***34", "confidence": 0.90}, {"label": "ANTHROPIC_API_KEY", "value": "sk-a***GH", "confidence": 0.90}, {"label": "HUGGINGFACE_TOKEN", "value": "hf_a***56", "confidence": 0.90} ]
Analysis:
- ✅ Our approach explicitly identifies Anthropic keys
- ✅ We have dedicated patterns for AI/ML providers
- ✅ Both detect OpenAI keys
Example 3: SVG File (False Positive Test)
Input File (icon.svg):
<svg viewBox="0 0 100 100"> <path d="M 10 20 L 30 40 L 50 60 L 70 80 L 90 100"/> <text font-size="12">Icon v1.2.3.4</text> <image href="data:image/png;base64,iVBORw0KGgoAAAANS..."/> </svg>
Our Detection:
[] // No false positives - SVG detection mode activated
Analysis:
- ✅ Our approach activates "minimal detection mode" for SVG files
- ✅ We filter out base64 image data and coordinates
- ⚠️ Traditional tools often flag base64 data as potential secrets
Performance Comparison
Speed Benchmarks
| Scenario | Our Approach | TruffleHog | Winner |
|---|---|---|---|
| Single file (1KB) | 0.002s | 0.01s | Ours |
| Medium repo (1000 files) | 2.5s | 15s | Ours |
| Large repo (10,000 files) | 25s | 180s | Ours |
| With ML enabled | 0.1s/file | N/A | TruffleHog |
Accuracy Benchmarks
| Metric | Our Approach | TruffleHog (unverified) |
|---|---|---|
| Precision | 99.2% | 90-95% |
| Recall | 98.3% | 88-92% |
| F1 Score | 98.7% | 91-93% |
| False Positive Rate | 1-3% | 5-10% |
When to Use Each
Choose Precogs Adaptive Intelligence When:
- Real-time scanning needed - Faster regex-first detection
- AI/ML API keys are common - Better coverage for OpenAI, Anthropic, etc.
- SVG/XML files in codebase - Context-aware false positive reduction
- Integration with compliance frameworks - Built-in GDPR, HIPAA, SOX mapping
- Enterprise credential enrichment - Identity and permission lookup
- Web UI needed - Interactive scanning and results
The Bottom Line
| Criteria | Winner | Notes |
|---|---|---|
| Speed | Our Approach | 10x faster for large repos |
| AI/ML Keys | Our Approach | More explicit patterns |
| False Positives | Our Approach | Context-aware filtering |
| SVG/XML Files | Our Approach | Minimal detection mode |
| Compliance | Our Approach | 7 frameworks mapped |
| Enterprise | Our Approach | Credential enrichment |
Precogs Adaptive Intelligence excels at fast, context-aware security with lower noise. For modern production environments, Precogs Priority delivers the speed and precision required for real-time protection.
Explore the Precogs AI Data Security Series
-
PII Detection Guide: Adaptive Intelligence vs. Static Patterns
-
Automotive PII Detection: Securing VIN, IMEI, and Telematics Data
Getting Started with Precogs Priority
Never leak a secret again. Start scanning your repositories in seconds.
Explore the Precogs Platform: Learn how Precogs AI-native security helps detect sensitive data, vulnerabilities, and risks across your code and repositories.
Access the Precogs App: Sign in to the Precogs platform and start scanning your repositories.
Connect Your Repositories: Integrate your GitHub, GitLab, or Bitbucket repositories and let Precogs automatically analyze your code, history, and artifacts for security and data risks.
Flexible Deployment Options: Precogs supports cloud, private cloud, and on-premise deployments for organizations with strict security or data residency requirements. Contact our team to learn more.

